Reproductive Data Privacy Guide: What You Need to Know
In the era of “Quantified Self,” we track everything. Our steps, our calories, and for millions of women, our menstrual cycles. It used to be convenient. Now, in a shifting…
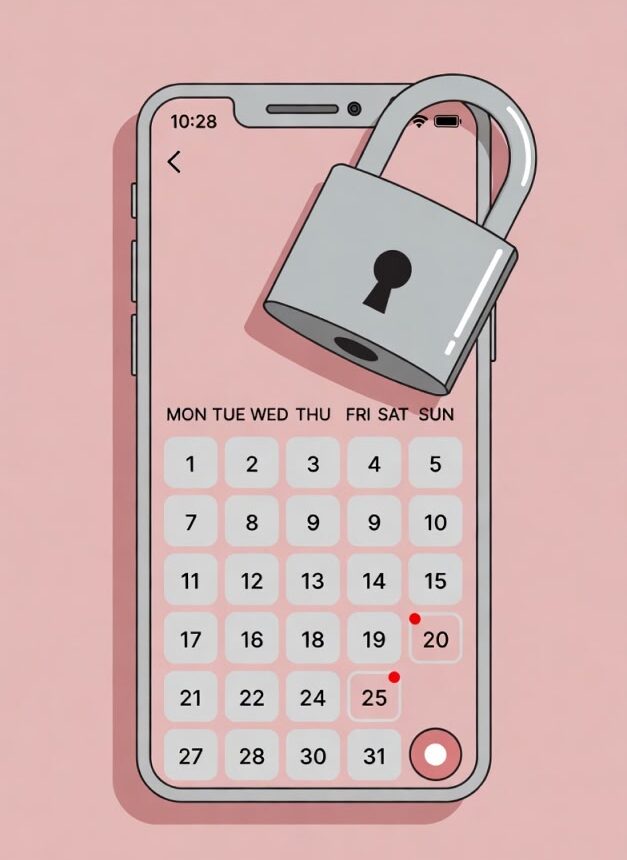
In the era of “Quantified Self,” we track everything. Our steps, our calories, and for millions of women, our menstrual cycles. It used to be convenient. Now, in a shifting legal landscape regarding reproductive rights, that data is potentially radioactive.
And the companies collecting it? They aren’t your friends. They are data hoarders.
The Risk: They Know Before You Do
You might think, “I don’t log my pregnancy status, so I’m safe.” Don’t be naive. Modern algorithms are incredibly good at inference:
- A sudden change in resting heart rate?
- A consistent rise in basal body temperature?
- A cessation of logged menstrual cycles?
Combined, these data points can flag a user as “likely pregnant” to advertisers (and potentially data brokers) long before you even buy a crib. It is creepy, it is invasive, and it happens in the background.
The “Recovery” Trap
This is where general fitness trackers (like the ones mentioned in our WHOOP lawsuit coverage) come in.
Even if you aren’t using a dedicated period tracker, these devices monitor “Recovery” or “Readiness” scores. A pregnancy often manifests as a prolonged period of “low recovery” or elevated heart rate.
If this data is shared with third parties for “analytics,” you have a privacy leak you didn’t even know about.
Actionable Advice: The 3-Step Audit
- The “Sell” Test
Read the Privacy Policy. Search for the word “Sell.” If the policy says “We do not sell your data,” look for the asterisk. Does it say “We may share data with trusted partners for marketing purposes”? That is effectively the same thing. It’s wordplay designed to fool you. - Turn on End-to-End Encryption (E2EE)
Some apps, like Clue or Flo (in “Anonymous Mode”), offer features where the company itself cannot read your data—it is encrypted on your device. If your app does not offer E2EE, assume the data is accessible to them, their partners, and anyone with a subpoena. - Use a Pseudonym
If you must use a tracker, do not link it to your primary email or social media accounts. Create a burner email address.
The Bottom Line
Your biological data is the most intimate thing you own. Don’t trade it for a “wellness score” without reading the fine print.
And if you want to know what else you’re blindly agreeing to, check out our List of 5 Terms of Service Red Flags.
Been harmed by corporate negligence? Our legal partners can help you understand your rights and pursue justice.




 Written by: Companies Behaving Badly
Written by: Companies Behaving Badly